docker run --name freeipa-server-container -it \ -h server.freeipa.local -e PASSWORD=YOUR_PASSWORD \ -v /sys/fs/cgroup:/sys/fs/cgroup:ro \ -v /var/lib/ipa-data:/data:Z adelton/freeipa-server
SSSD and FreeIPA Identity Management Integration
Keycloak also comes with a built-in SSSD (System Security Services Daemon) plugin. SSSD is part of the latest Fedora or Red Hat Enterprise Linux and provides access to multiple identity and authentication providers. It provides benefits such as failover and offline support. To see configuration options and for more information see the Red Hat Enterprise Linux Identity Management documentation.
SSSD also integrates with the FreeIPA identity management (IdM) server, providing authentication and access control. For {book_project_name}, we benefit from this integration authenticating against PAM services and retrieving user data from SSSD. For more information about using Red Hat Identity Management in Linux environments, see the Red Hat Enterprise Linux Identity Management documentation.
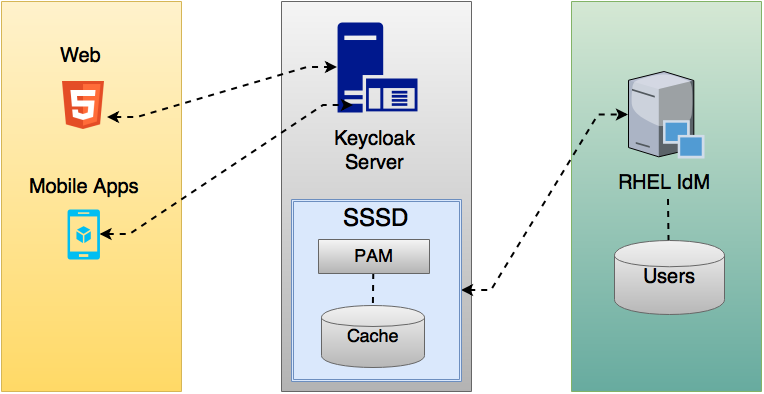
Most of the communication between Keycloak and SSSD occurs through read-only D-Bus interfaces. For this reason, the only way to provision and update users is to use the FreeIPA/IdM administration interface. By default, like the LDAP federation provider, it is set up only to import username, email, first name, and last name.
|
Note
|
Groups and roles are automatically registered, but not synchronized, so any changes made by the Keycloak administrator directly in Keycloak is not synchronized with SSSD. |
Information on how to configure the FreeIPA/IdM server follows.
FreeIPA/IdM Server
As a matter of simplicity, a FreeIPA Docker image already available is used. To set up a server, see the FreeIPA documentation.
Running a FreeIPA server with Docker requires this command:
The parameter -h with server.freeipa.local represents the FreeIPA/IdM server hostname. Be sure to change YOUR_PASSWORD to a password of your choosing.
After the container starts, change /etc/hosts to:
x.x.x.x server.freeipa.local
If you do not make this change, you must set up a DNS server.
So that the SSSD federation provider is started and running on Keycloak you must enroll your Linux machine in the IPA domain:
ipa-client-install --mkhomedir -p admin -w password
To ensure that everything is working as expected, on the client machine, run:
kinit admin
You should be prompted for the password. After that, you can add users to the IPA server using this command:
$ ipa user-add john --first=John --last=Smith [email protected] --phone=042424242 --street="Testing street" \ --city="Testing city" --state="Testing State" --postalcode=0000000000
SSSD and D-Bus
As mentioned previously, the federation provider obtains the data from SSSD using D-BUS and authentication occurs using PAM.
First, you have to install the sssd-dbus RPM, which allows information from SSSD to be transmitted over the system bus.
$ sudo yum install sssd-dbus
You must run the provisioning script available from the Keycloak distribution:
$ bin/federation-sssd-setup.sh
This script makes the necessary changes to /etc/sssd/sssd.conf:
[domain/your-hostname.local] ... ldap_user_extra_attrs = mail:mail, sn:sn, givenname:givenname, telephoneNumber:telephoneNumber ... [sssd] services = nss, sudo, pam, ssh, ifp ... [ifp] allowed_uids = root, yourOSUsername user_attributes = +mail, +telephoneNumber, +givenname, +sn
Also, a keycloak file is included under /etc/pam.d/:
auth required pam_sss.so account required pam_sss.so
Ensure everything is working as expected by running dbus-send:
sudo dbus-send --print-reply --system --dest=org.freedesktop.sssd.infopipe /org/freedesktop/sssd/infopipe org.freedesktop.sssd.infopipe.GetUserGroups string:john
You should be able to see the user’s group. If this command returns a timeout or an error, it means that the federation provider will also not be able to retrieve anything on Keycloak.
Most of the time this occurs because the machine was not enrolled in the FreeIPA IdM server or you do not have permission to access the SSSD service.
If you do not have permission, ensure that the user running Keycloak is included in the /etc/sssd/sssd.conf file in the following section:
[ifp] allowed_uids = root, your_username
Enabling the SSSD Federation Provider
Keycloak uses DBus-Java to communicate at a low level with D-Bus, which depends on the Unix Sockets Library.
An RPM for this library can be found in this repository. Before installing it, be sure to check the RPM signature:
$ rpm -K libunix-dbus-java-0.8.0-1.fc24.x86_64.rpm libunix-dbus-java-0.8.0-1.fc24.x86_64.rpm: Header V4 RSA/SHA256 Signature, key ID 84dc9914: OK Header SHA1 digest: OK (d17bb7ebaa7a5304c1856ee4357c8ba4ec9c0b89) V4 RSA/SHA256 Signature, key ID 84dc9914: OK MD5 digest: OK (770c2e68d052cb4a4473e1e9fd8818cf) $ sudo yum install libunix-dbus-java-0.8.0-1.fc24.x86_64.rpm
For authentication with PAM Keycloak uses JNA. Be sure you have this package installed:
$ sudo yum install jna
Configuring a Federated SSSD Store
After installation, you need to configure a federated SSSD store.
To configure a federated SSSD store, complete the following steps:
-
Navigate to the Administration Console.
-
From the left menu, select User Federation.
-
From the Add Provider dropdown list, select sssd. The sssd configuration page opens.
-
Click Save.
Now you can authenticate against Keycloak using FreeIPA/IdM credentials.